Avid long term readers may remember our last examination of an internet aware sex toy and how it could be used by the NSA to really really invade your privacy. Indeed one avid reader remembered so vividly that they tipped us of to this latest entry of a sex toy into the internet of things, or as we are calling this growing technology sector, the internet of bad bad dirty things. This one is an internet aware, blue tooth enabled buttplug. A presentation on the ahem, penetration hacking, of the so-called “Hush” model of buttplugs made by Lovesense was made at this year's premier hacking convention at the Paris Hotel and Casino in Las Vegas.
The public needs to be made aware of privacy implications of an internet aware device in the anus so this time a hack happening in Vegas will not stay in Vegas. The company has not commented on their cheaply made software nor have the full privacy implications of a device that can have it's security ahem violated been addressed.
The Hush is a buttplug that is controlled via a bluetooth dongle attached to a laptop. It can be controlled directly from across the room or remotely via an internet connection with another computer and a chat session, either through the company's proprietary software or a third party chat program like Skype, which has built in security holes for direct exploitation, or WhatsApp, which is also known to be vulnerable.
The security hole at the bluetooth level allows remote execution of code on the host computer via the dongle and on the physical device. Using such a device would allow a bluetooth based attack on one's laptop while the use is, shall we say, somewhat distracted. Should the user not be sufficiently distracted for malware, surveillance tools or ransomware to be inserted onto their computer, remote execution of code on the physical device might divert their attention.
The security holes come from a known weaknesses in the actual chipset used in the motor controller, another in Bluetooth's low power library of functions, and in Electron, the open source software suite used to program the remote application, which is java script based. This creates the perfect storm for someone to get their virtual self into a place that they were not invited.
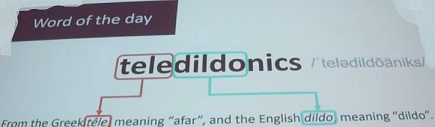
Somehow Lovesense thinks that what they do is a science which they call teledildonics. This author is not sure if calling that a science is more ridiculous than highlighting that word and clicking on “add to dictionary.” These possible hacks are actually dangerous, as they can override safety features. According to “Smea”, the security researcher who presented these problems, this is not so bad with Hush as an override of motor controls will not produce dangerous results, but could be an actual health threat when applied to a sex toy with a motor that moves rotating parts, like the same company's “Nora” model of rabbit vibrator for women.
Teledildonics, as a science, is clearly in it's infancy. In addition to endangering thousands in rushing their products to market with more security holes than a screen door on a bank vault, Lovesense either failed to note or failed to inform ahem end users ahem of the government level privacy implications under the Patriot Act.
The Patriot Act contains many provisions, but the one noteworthy under this context is Section 215(a), the so-called business records provision. This allows the federal government to call something a terrorism related investigation and seize any and all records of any business related to that investigation. When those business records include chat logs and biometric data from a proprietary chat application used in conjunction with biometric data in the context of remote sexual activity, one can see the many ways this can be used for blackmail, and that is just for starters. This author can think of no greater violation of privacy than the NSA literally having a biometric sensor up your butt while listening in on your sexy time.
Section 215(a) can be combined with hacking in more sinister ways with the aforementioned security hole that allow a remote attacker to bypass safety stops on motor controls. This technology could be used by a joint NSA-CIA team like the one Edward Snowden worked on before he was a whistle blower to literally fuck you to death.
Some things are best done in person, and sex is one of them. The Mockingbird encourages users to have a healthy and fulfilling sex life without the possibility of involving hackers and government agents.
